Cybersecurity is no longer a purely technical discipline. It has become a fundamental business capability that protects revenue, operations, intellectual property, and reputation.
As organizations expand their digital footprint across cloud infrastructure, SaaS platforms, connected devices, and distributed workforces, the attack surface grows accordingly.
Comprehensive cybersecurity services exist to manage that reality. They combine people, processes, and technology to reduce cyber risk, detect threats early, and maintain operational continuity.
At the same time, modern programs increasingly incorporate AI-driven analytics to improve detection accuracy, prioritize alerts, and accelerate response to emerging threats.
The objective is not only to prevent attacks. The real goal is to build resilient systems that allow organizations to operate, innovate, and scale while managing cyber risk in a structured and measurable way.
Executive Summary: Cybersecurity Services and Cyber Risk
Cybersecurity services are designed to protect business-critical systems and data from evolving cyber threats while enabling operational continuity.
Effective cybersecurity programs combine several capabilities within a unified framework:
• Governance
• Monitoring
• Incident response
• Identity management
• Vulnerability management
This approach allows organizations to reduce exposure to cyber risk while maintaining the agility required for digital transformation.
In practice, cybersecurity programs must achieve two outcomes simultaneously:
• Protect critical assets
• Support business innovation
Understanding Cyber Threats and Cybersecurity Challenges
Cyber threats have evolved significantly over the past decade. Attackers now operate with professional structures, automation, and sophisticated tools.
One of the most persistent entry points remains phishing. These social engineering attacks exploit human behavior and frequently lead to credential compromise or ransomware deployment.
At the same time, supply-chain risk has increased. Organizations depend on third-party software, APIs, and service providers, which can introduce indirect vulnerabilities into otherwise secure environments.
In more advanced scenarios, nation-state and organized criminal groups target intellectual property, critical infrastructure, and sensitive corporate data. These campaigns often operate quietly over extended periods.
For leadership teams, the implication is clear: cybersecurity strategies must address both internal vulnerabilities and external dependencies across the digital ecosystem.
Cyber Risk Assessments, Threat Modeling, and Compliance
Effective cybersecurity begins with a clear understanding of risk.
Cyber risk assessments evaluate business systems, data assets, and operational processes to determine where security failures could have the greatest business impact.
This allows organizations to prioritize controls based on asset criticality and realistic threat scenarios.
Threat modeling complements this process by identifying potential attack paths across applications, infrastructure, and cloud environments.
Organizations must also align cybersecurity controls with recognized frameworks and regulatory standards, such as:
• NIST Cybersecurity Framework
• ISO 27001
• PCI DSS
• Regional cybersecurity and data protection regulations
Compliance alone does not guarantee security. However, it provides structure, accountability, and governance within a cybersecurity program.
Core Cybersecurity Services
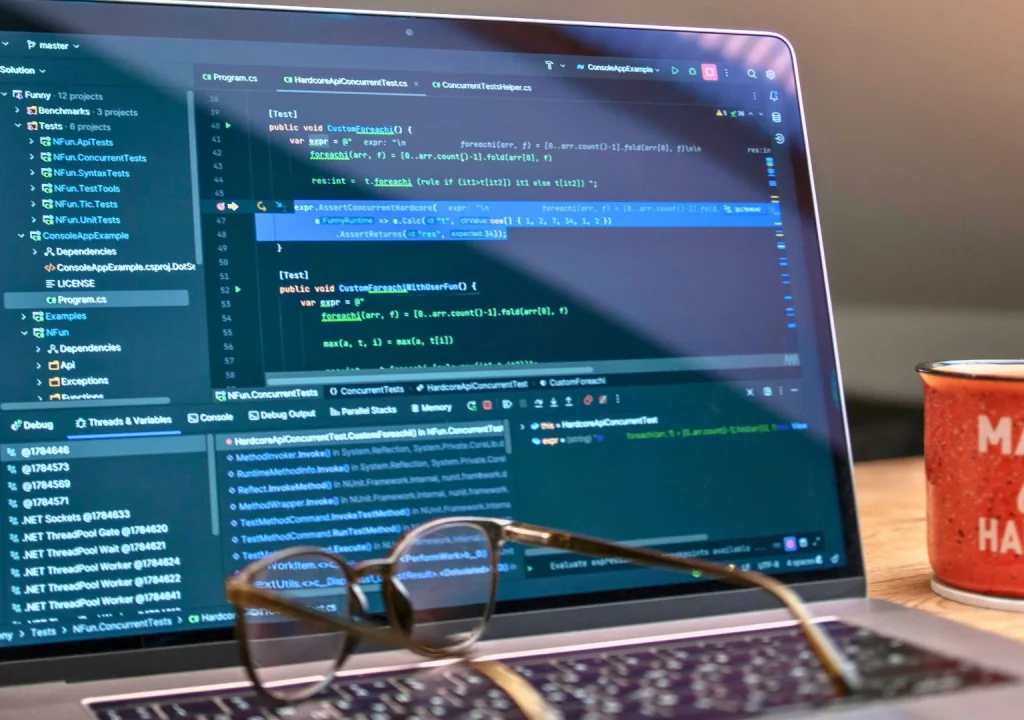
Most modern cybersecurity programs rely on a set of foundational operational services.
Managed Detection and Response (MDR) provides continuous monitoring across endpoints, networks, and cloud systems. By aggregating telemetry from multiple sources, MDR improves early detection and rapid containment of suspicious activity.
Threat intelligence and proactive threat hunting focus on identifying attacker behavior before it escalates into a breach.
Vulnerability management programs continuously identify weaknesses in systems and applications, prioritizing remediation based on risk severity and exploitability.
Finally, security orchestration and automation improve operational efficiency by automating containment workflows and reducing manual incident response effort.
Together, these capabilities form the operational backbone of modern cyber defense.
Managed Cyber Defense and SOC Services
Many organizations rely on Security Operations Centers (SOC) to monitor threats continuously and coordinate response activities.
A modern SOC integrates several capabilities:
• Advanced analytics to detect anomalous behavior
• Security orchestration platforms (SOAR) that automate response actions
• Security analysts who investigate and validate alerts
Integrating telemetry from endpoints, networks, and cloud environments improves detection accuracy while reducing false positives.
However, effective SOC operations require constant tuning. Detection rules, analytics models, and response playbooks must evolve alongside attacker techniques.
Incident Response, Forensics, and Recovery
Even mature cybersecurity programs must assume that security incidents will occur.
Incident response teams focus on containing the attack, removing threats from the environment, and restoring systems safely.
During this process, forensic evidence is preserved to determine the root cause of the incident.
Rapid response significantly reduces operational disruption and recovery time following ransomware attacks or data breaches.
After recovery, post-incident analysis helps organizations identify control gaps and strengthen defenses against future threats.
Many organizations also conduct tabletop exercises to simulate high-severity incidents and validate leadership decision-making and communication procedures.
Cloud Security and DevSecOps
As organizations migrate workloads to cloud platforms, security responsibilities shift but remain critical.
Cloud security services protect workloads, identities, and configurations across IaaS, PaaS, and SaaS environments.
Monitoring configurations and enforcing access policies helps reduce the likelihood of misconfigurations that expose sensitive data.
At the development level, DevSecOps practices integrate automated security testing into CI/CD pipelines, allowing vulnerabilities to be identified early in the development lifecycle.
Additional controls such as cloud posture management, encryption, and workload isolation further reduce the impact of compromised cloud assets.
Identity, Access Management, and Zero Trust
Identity has become the new security perimeter.
Traditional network-based models assumed that users inside the network could be trusted. Modern environments require continuous verification.
Identity and Access Management (IAM) systems enforce least-privilege policies, ensuring users only have the permissions required to perform their roles.
Zero Trust architectures extend this concept by requiring continuous authentication and risk-based verification before granting access to sensitive systems.
Strong authentication combined with adaptive access policies significantly reduces the risk of credential compromise and lateral movement within networks.
Vulnerability Management and Penetration Testing
No system is completely free of vulnerabilities. The key is identifying weaknesses before attackers exploit them.
Continuous vulnerability scanning identifies outdated software, configuration errors, and known security flaws.
However, automated scanning alone is not enough. Penetration testing simulates attacker behavior to uncover chained exploit paths that automated tools might miss.
Organizations seeking deeper insight often conduct red team engagements, which simulate persistent attackers attempting to bypass detection and response capabilities.
These exercises provide valuable insight into both technical defenses and organizational readiness.
Critical Infrastructure and Operational Technology Security
Operational technology (OT) environments—including manufacturing systems, industrial networks, and energy infrastructure—present unique cybersecurity challenges.
In these environments, availability and operational safety are often more critical than data confidentiality.
OT security programs typically focus on:
• Asset visibility across industrial systems
• Network segmentation between IT and OT environments
• Secure remote access for operators and vendors
These measures help reduce the operational impact of cyber incidents affecting physical infrastructure.
AI-Enabled Cybersecurity Solutions
AI-driven detection systems analyze large volumes of security telemetry to identify patterns and anomalies that indicate malicious activity.
This capability is particularly valuable in environments where millions of security events are generated daily.
AI also improves alert prioritization, allowing analysts to focus on high-risk threats instead of low-value alerts. This significantly reduces analyst fatigue and improves response efficiency.
AI also improves alert prioritization, allowing analysts to focus on high-risk threats instead of low-value alerts. This significantly reduces analyst fatigue and improves response efficiency.
However, AI models require continuous monitoring and validation to prevent model drift and maintain detection accuracy.
Cybersecurity Solutions for Industry-Specific Needs
Different industries face different cybersecurity risks.
• Financial institutions prioritize fraud prevention and transaction integrity.
• Healthcare organizations focus on patient privacy and medical device security.
• Energy and utility companies emphasize infrastructure resilience and operational continuity.
Industry-specific cybersecurity programs ensure security controls align with both regulatory requirements and operational realities.
Governance, Risk, and CISO Advisory Services
Cybersecurity must align with broader business strategy.
CISO advisory services help organizations design security programs that support business objectives while meeting regulatory obligations and budget constraints.
Risk governance frameworks establish clear structures for defining risk tolerance, measuring exposure, and reporting cybersecurity performance to leadership.
Vendor risk management programs also evaluate the security posture of third-party providers, ensuring external partners meet appropriate cybersecurity standards.
Measuring Security Effectiveness
Cybersecurity performance must be measurable.
Two widely used operational metrics include:
• Mean Time to Detect (MTTD)
• Mean Time to Respond (MTTR)
These indicators measure how quickly organizations can identify and contain threats.
Beyond operational metrics, control effectiveness assessments evaluate whether implemented controls actually reduce measurable cyber risk.
Delivery Models: Managed Services, Consulting, and Productized Solutions
Organizations typically adopt a combination of delivery models depending on internal capabilities.
Managed cybersecurity services provide continuous monitoring, detection, and response.
Consulting engagements focus on targeted initiatives such as architecture redesign, compliance remediation, or incident response preparation.
Productized cybersecurity solutions package repeatable services—such as cloud hardening, identity management deployments, or incident response retainers—into structured offerings that accelerate implementation.
Implementation Considerations and Procurement Signals
Implementing cybersecurity capabilities requires careful planning.
Many organizations begin with proof-of-value pilots to demonstrate improvements in detection accuracy or remediation speed before committing to enterprise-wide deployment.
Integration with existing systems:
• SIEM
• Indentity Providers
• Cloud Infrastructure
Service agreements should clearly define expectations, including:
• Incident response service-level agreements
• Data handling and retention policies
• Third-party disclosure responsibilities
Conclusion: Cybersecurity as a Strategic Capability
Cybersecurity has evolved from a defensive IT function into a strategic business capability.
Organizations that treat cybersecurity as an integrated component of digital operations—rather than a reactive technical measure—are better positioned to manage risk while continuing to innovate.
Effective programs combine governance, monitoring, cloud security, identity protection, and AI-driven analytics within a structured framework.
The objective is not to eliminate risk entirely. Instead, organizations must understand risk, prioritize controls, and build systems capable of detecting, responding to, and recovering from cyber incidents without disrupting business operations.
Strengthen Your Cybersecurity Strategy
Improving cybersecurity begins with understanding the current state of your security posture.
HitOcean works with organizations to assess cyber risk, design security architectures, and implement AI-driven cybersecurity solutions aligned with business objectives and regulatory requirements.
Whether your organization is strengthening cloud security, implementing Zero Trust architecture, building a SOC capability, or preparing for regulatory compliance, a structured cybersecurity strategy can significantly reduce risk while supporting long-term digital growth.
If your organization is evaluating how to improve resilience against evolving cyber threats, HitOcean can help define a clear and practical roadmap toward a stronger cybersecurity posture.